There was a report in May 2025 of information leakage when using O2 UK’s IMS services on a Pixel 9:
https://mastdatabase.co.uk/blog/2025/05/o2-expose-customer-location-call-4g/
SIP Message
…
P-Mav-Extension-IMSI: 23410123456789
P-Mav-Extension-IMSI: 23410987654321
P-Mav-Extension-IMEI: 350266809828927
P-Mav-Extension-IMEI: 350266806365261
…
Cellular-Network-Info: 3GPP-E-UTRAN-FDD;utran-cell-id-3gpp=2341010037A60773;cell-info-age=26371
“Two sets of IMSIs, two sets of IMEIs, and a Cell ID header. How curious… Sure enough, when comparing both the IMSIs and IMEIs in the message to those of my own devices, I had been given both the IMSI and IMEI of my phone which initiated the call, but also the call recipient’s.”
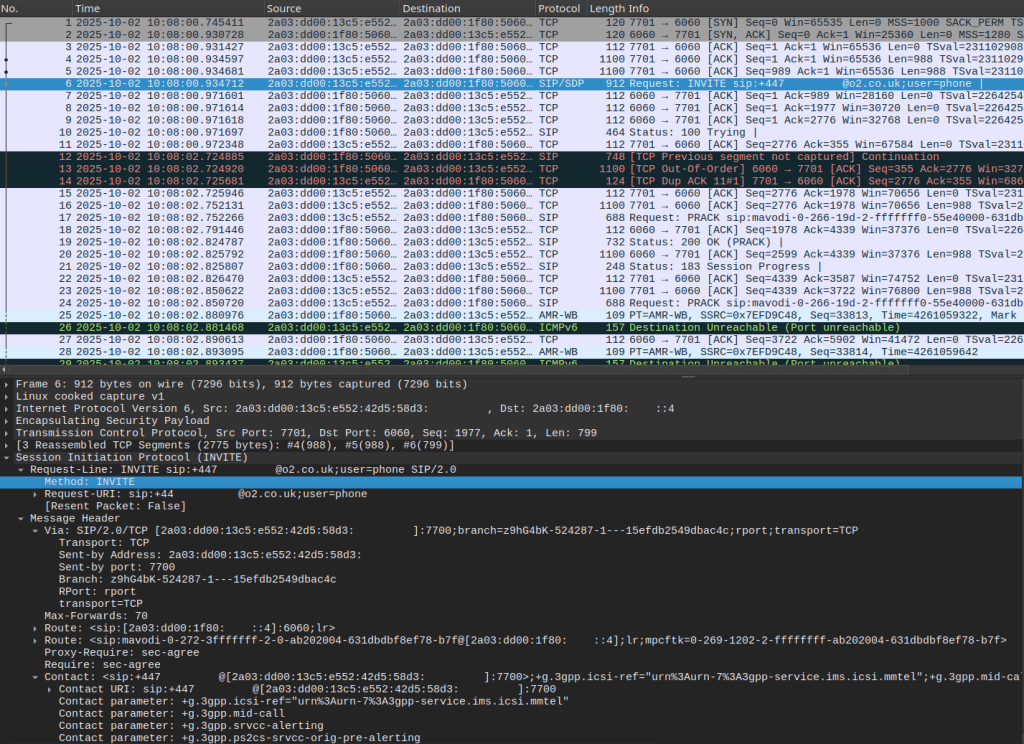
Q-Performance captures SIP traces for VoLTE and VoWiFi. Therefore, users can explore historical traces and investigate this type of issue by downloading the PCAP files.
This provides an independent and objective view, along with a wealth of SIP and TCP data:

Leave a comment